Видео с ютуба Secure Computation

Introducing Secure Multi Party Computation (MPC)

How secure is 256 bit security?

Secure Multi-party Computation - Secure Circuit Evaluation Explained

Secure Multi-party Quantum Computation with a Dishonest Majority

"Secure-computation AI" secure computation for a typical training algorithm of a deep neural network

Secure Computation in Computing

USENIX Security '21 - Fantastic Four: Honest-Majority Four-Party Secure Computation With Malicious
![Towards more Practical Secure Computation: Efficient Protocols for Secure Linear Algebra [1/2]](https://imager.clipsaver.ru/Hs-7ixoSqAA/max.jpg)
Towards more Practical Secure Computation: Efficient Protocols for Secure Linear Algebra [1/2]

What is Secure Multiparty Computation (MPC)?

Secure Multi-party Computation. Recent Advances and Current Applications

GraphSC: Parallel Secure Computation Made Easy

Secure multi-party computation

Secure Multi-party Quantum Computation with a Dishonest Majority

Geometry of Secure Computation

EzPC (Easy Secure Multi-party Computation)
![[MPC][Mike Rosulek]Lecture 1-3: Overview of Secure Computation and Yao's Protocol](https://imager.clipsaver.ru/4jZcGqgZKY8/max.jpg)
[MPC][Mike Rosulek]Lecture 1-3: Overview of Secure Computation and Yao's Protocol

SoK: General Purpose Frameworks for Secure Multi-Party Computation

Fast Secure Computation for Small Population over the Internet
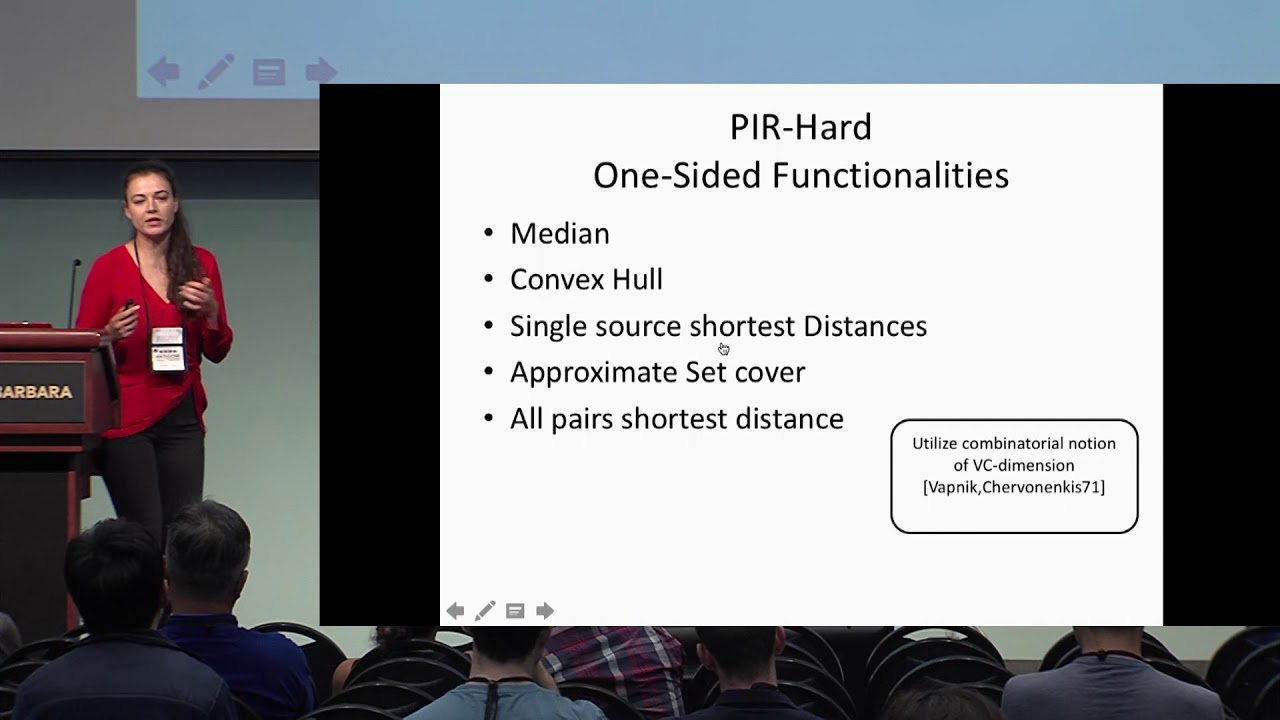
Limits of Practical Sublinear Secure Computation

Secure Computation 3